Enhance Data Security With Trusted Cloud Services
In today's interconnected electronic landscape, the value of boosting data safety with trusted cloud services can not be overemphasized. As organizations browse the intricacies of safeguarding delicate details, the dependence on safe and secure cloud options becomes an essential method. By handing over information to respectable cloud service providers geared up with innovative safety procedures, services can fortify their defenses against cyber dangers and make sure information confidentiality. The inquiry stays: Exactly how can companies effectively navigate the myriad of alternatives readily available and choose a reputable cloud service provider that aligns with their safety needs?
Relevance of Information Protection
Making certain durable data safety procedures is extremely important in today's electronic landscape to safeguard delicate details from unapproved accessibility and cyber hazards. With the rapid development of information generation and storage, companies face boosting challenges in safeguarding their beneficial possessions. Data violations not only lead to monetary losses yet also harm a company's credibility and wear down consumer trust.
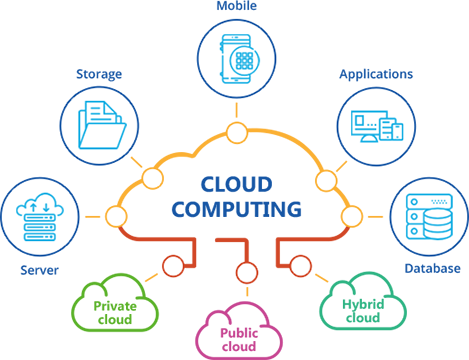
In the present era of remote work and cloud computer, the significance of information safety is better magnified. Cloud services offer scalability, cost-efficiency, and adaptability, but without sufficient safety and security steps, they can posture considerable risks. Companies must focus on data protection when embracing cloud solutions to avoid data breaches and support the integrity of their procedures (universal cloud Service).
Advantages of Trusted Cloud Services
Provided the climbing relevance of data safety in the electronic landscape, recognizing the advantages of trusted cloud services ends up being vital for companies aiming to strengthen their information security methods. Relied on cloud solutions offer countless benefits that can boost information protection actions. These solutions supply robust file encryption procedures, ensuring that information is safely saved and transmitted. This security helps avoid unauthorized access, decreasing the danger of information violations.

In addition, relied on cloud solutions supply reliable backup and catastrophe recovery services, ensuring data availability even in the event of unexpected events. This integrity is vital for maintaining service connection and minimizing information loss. Overall, the benefits of relied on cloud services add dramatically to strengthening data safety and security practices within companies.
Key Features of Secure Cloud Solutions
Applying durable safety steps is necessary in making certain the honesty of information saved and transferred with cloud solutions. Additionally, protected cloud remedies provide multi-factor authentication, needing users to supply multiple kinds of verification prior to accessing the data. These features jointly contribute to an extra protected cloud environment, instilling confidence in users regarding the protection of their information.
Finest Practices for Information Security
To fortify data protection in cloud environments, sticking to finest techniques for information protection is vital. File encryption plays an essential duty in protecting delicate info saved in the cloud. Carrying out file encryption mechanisms, both at rest and in transportation, makes certain that information is muddled to unapproved customers even if it is intercepted. Access control is another necessary practice for information defense. By imposing rigorous access controls, companies can limit that can view, modify, or delete data, decreasing the risk of unapproved accessibility. Routinely supporting information is likewise an essential element of data protection. In case of information loss or useful content a protection violation, having updated back-ups allows swift recuperation without compromising useful details. Furthermore, monitoring and bookkeeping data access and use help in detecting any dubious activities promptly. By following these best practices for data security, organizations can improve their data safety and security pose in the cloud setting.
Picking a Reliable Cloud Provider
Choosing a trustworthy cloud provider is an essential choice for organizations looking for to enhance their information protection procedures. When picking a cloud supplier, a number of essential elements need to be taken into consideration to make sure reliability. To start with, companies should analyze the provider's protection measures, consisting of data security, access controls, and compliance certifications. A trustworthy cloud company must have durable protection methods in location to safeguard information versus unapproved gain access to and cyber risks.
In addition, companies must assess the provider's directory uptime and dependability performance history. Downtime can have substantial effects for service operations and information access, so picking a provider with a tried and tested record of high uptime is essential. Additionally, organizations need to take into consideration the scalability and flexibility offered by the cloud carrier to suit future development and changing service demands.
Lastly, assessing the supplier's customer support services is essential. In case of any kind of issues or safety breaches, knowledgeable and responsive client support can make a substantial difference in mitigating risks and guaranteeing prompt resolutions. By meticulously considering these aspects, organizations can select a reliable cloud company that fulfills their data security needs efficiently.
Final Thought
In final thought, leveraging relied on cloud services is vital for improving information protection in today's electronic landscape. By implementing durable security procedures, advanced threat discovery abilities, and reliable back-up solutions, companies can properly safeguard valuable information and minimize dangers of information breaches. Selecting a dependable cloud carrier and adhering to finest practices for data protection are important actions in maintaining data stability and making sure thorough defense against cyber dangers.
By delegating information to trusted cloud suppliers outfitted with cutting-edge security procedures, services can strengthen this hyperlink their defenses versus cyber threats and ensure data discretion. Organizations need to focus on data safety when adopting cloud services to stop information breaches and support the honesty of their operations.
Provided the rising importance of data safety and security in the digital landscape, comprehending the benefits of trusted cloud services ends up being important for organizations aiming to fortify their information defense strategies.To fortify information safety in cloud environments, sticking to ideal practices for data defense is paramount. By adhering to these ideal practices for information security, companies can improve their information protection pose in the cloud setting.